A unique and specific authentication key
When you scan your hand, it generates a unique cryptographic lock that is tied specifically to you, using your hand as the starting point. In essence, your hands act as both the public and private keys in the authentication process. No additional information is needed for authentication.
This method relies solely on your hand's physical features (both internal and external, including vein patterns and blood flows) and can function without requiring any personal identification, unless necessary.
No biometric databases are used,
no image or minutia comparisons are made,
no biometrics references are
archived.
The Veintree authentication system quickly observes your palm, scans and analyzes the image and biometric flows of your venous network, and then uses the data from this temporary reading to activate Veintree-developed calculation algorithms.
Once
the biometric reading has served its purpose, it is immediately deleted in order to
protect your identity.
Veintree's secure servers do not store any biometric
data. No reference databases are used, no image comparisons are made, no biometrics are archived.
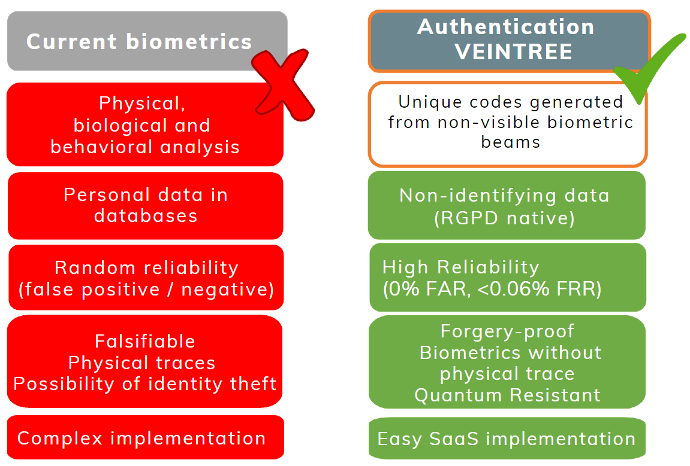

Authentication is dissociated from identification
Normally,
as a basic principle, authentication is dissociated from the identification of the person.
However, for use cases or environments where personal identification is
required for authentication, this aspect and information related to it are managed
internally by the company or organization (governmental or otherwise) using the
Veintree authentication system, and not by Veintree itself.
Veintree's
role is solely to authenticate that you are an authorized person who is entitled to
the services corresponding to your request, your access rights or your transactions, the purpose is not to
identify you. Our role is authentication, not identification.
Encryption is achieved without transmitting biometric data
Unique
dynamic coding and encryption are calculated locally on the device used. This
encrypted result is communicated to Veintree servers installed at customer
sites, which analyze the unique code that has been received and accept or reject the
authentication.
In all cases, the infrared image of your hand and the biometric
data that was captured are destroyed immediately once the encrypted code has been generated, thus ensuring the person's anonymity.
Even the code itself will be eliminated, since it
is designed for one-time use only.


Using sunlight for multi-spectral infrared illumination
In
practice, a smartphone camera, capable of detecting certain infrared wavelengths, scans
your palm and captures the pattern of your venous network and blood flow.
This sensing equipment may be a tablet-style device, a small device attached to
your cell phone, or eventually a device directly integrated into most phones.
When conditions are sunny, natural light suffice, and there's no need to illuminate the palm.
Veintree
is a trusted third party and Web3 Oracle
that enables your digital transactions,
without
revealing your personal data